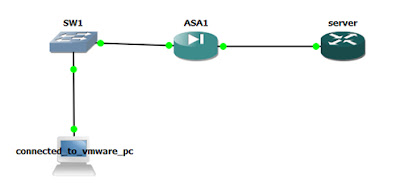
CISCO ASA Remote IPSEC VPN configuration, Example
ASA
| ||
Interface
|
E0 /0
|
E0/1
|
IP Address /
|
100.100.100.1
|
192.168.1.1
|
Net mask
|
255.255.255.0
|
255.255.255.0
|
Server Router
| ||
Interface
|
E1/0
| |
IP Address
|
192.168.1.10
| |
Net mask
|
255.255.255.0
| |
CISCO ASA CONFIGURATION
ciscoasa# show run
: Saved
:
ASA Version 8.0(2)
!
hostname ciscoasa
enable password 8Ry2YjIyt7RRXU24 encrypted
names
!
interface Ethernet0/0
nameif outside
security-level 0
ip address 100.100.100.1 255.255.255.0
no shut
!
interface Ethernet0/1
nameif inside
security-level 100
ip address 192.168.1.1 255.255.255.0
no shut
!
!
passwd 2KFQnbNIdI.2KYOU encrypted
ftp mode passive
access-list nonat extended permit ip 192.168.1.0 255.255.255.0 192.168.20.0 255.255.255.0
pager lines 24
mtu outside 1500
mtu inside 1500
ip local pool vpnpool 192.168.20.1-192.168.20.254
no failover
icmp unreachable rate-limit 1 burst-size 1
no asdm history enable
arp timeout 14400
timeout xlate 3:00:00
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout uauth 0:05:00 absolute
dynamic-access-policy-record DfltAccessPolicy
no snmp-server location
no snmp-server contact
snmp-server enable traps snmp authentication linkup linkdown coldstart
crypto ipsec transform-set ra-ts esp-3des esp-sha-hmac
crypto dynamic-map dyn-map 10 set transform-set ra-ts
crypto map vpn-map 30 ipsec-isakmp dynamic dyn-map
crypto map vpn-map interface outside
crypto isakmp enable outside
crypto isakmp policy 20
authentication pre-share
encryption 3des
hash sha
group 2
lifetime 3600
telnet timeout 5
ssh timeout 5
console timeout 0
threat-detection basic-threat
threat-detection statistics access-list
!
!
group-policy company-vpn-policy internal
group-policy company-vpn-policy attributes
dns-server value 192.168.1.6
vpn-idle-timeout 30
username user password 123456 encrypted
tunnel-group vpnclient type remote-access
tunnel-group vpnclient general-attributes
address-pool vpnpool
default-group-policy company-vpn-policy
tunnel-group vpnclient ipsec-attributes
pre-shared-key 1234
prompt hostname context
Cryptochecksum:00000000000000000000000000000000
: end
ciscoasa#
CISCO ROUTER CONFIGURATION
interface Ethernet1/0
ip address 192.168.1.10 255.255.255.0
no shut
ip route 0.0.0.0 0.0.0.0 192.168.1.1
line vty 0 4
password test
login
INSTALL VPN CLIENT ON VMAWARE MACHINE
FILL UP CONNECTION DETAIL
HOST: 100.100.100.1
SELECT GROUP AUTHENTICATION
NAME: VPNCLIENT
PASSWORD : 1234
CLICK SAVE AND CONNECT
ENTER USER NAME AND PASSWORD
Username: user
Password: 123456

No comments:
Post a Comment